Because reading JSON at 2 a.m. is a no-go.
Table of Contents
What is SARIF?
SARIF (Static Analysis Results Interchange Format) is a standardized JSON format used by static analysis tools to report their findings. Tools like semgrep and opengrep can output their results in SARIF, making it possible to process and visualize findings from different scanners in a unified way.
The problem? SARIF files are dense, deeply nested JSON. Scrolling through hundreds of findings in a raw JSON file or even in VSCode gets painful fast, especially when you need to triage, annotate, and track the status of each finding across a full audit.
Why this tool?
When I first became interested in code review, I came across a video by noraj explaining how to use semgrep to extract a sarif file and read it using vscode. I thought it was a smart idea and wanted to explore it further with my friend Claude Code, who immediately understood the concept. :))))
The idea
Instead of fighting with raw JSON, I wanted a proper web interface that turns SARIF output into an actionable todo list, something where you can drag-and-drop your file, browse findings visually, and track your progress through an audit.
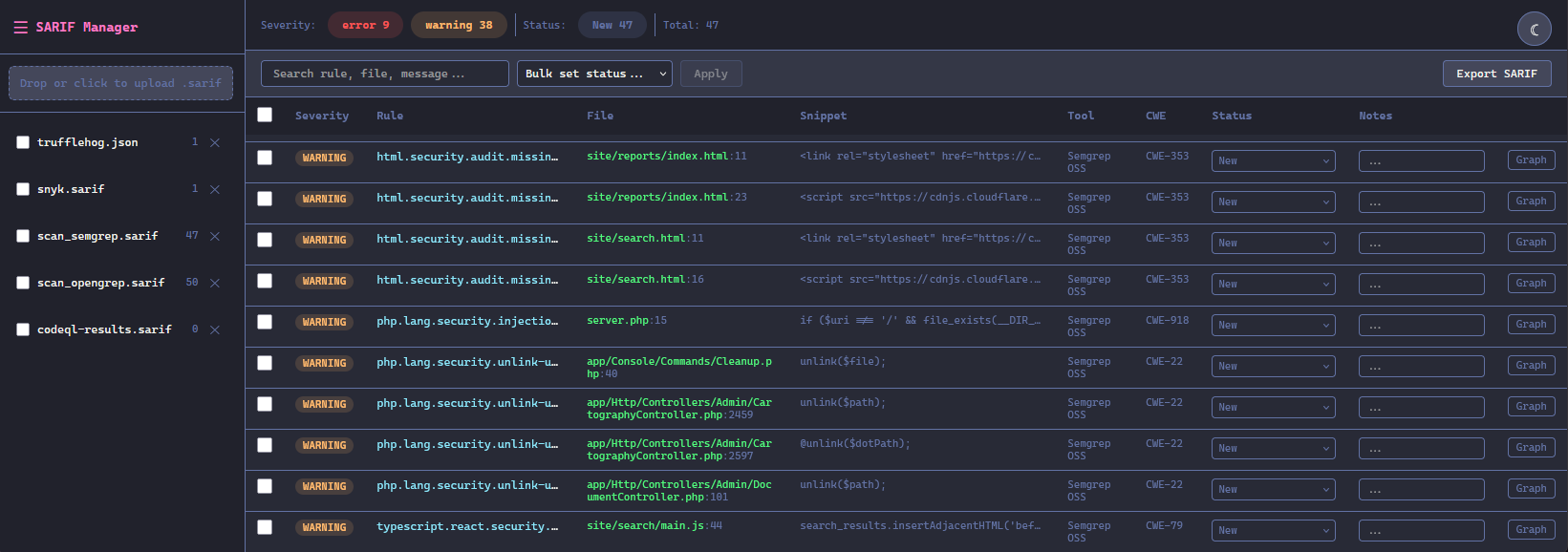
The main dashboard supports multiple SARIF projects side by side and gives you a sortable, filterable table of all findings with their severity, rule, file location, code snippet, tool, CWE, status, and notes:
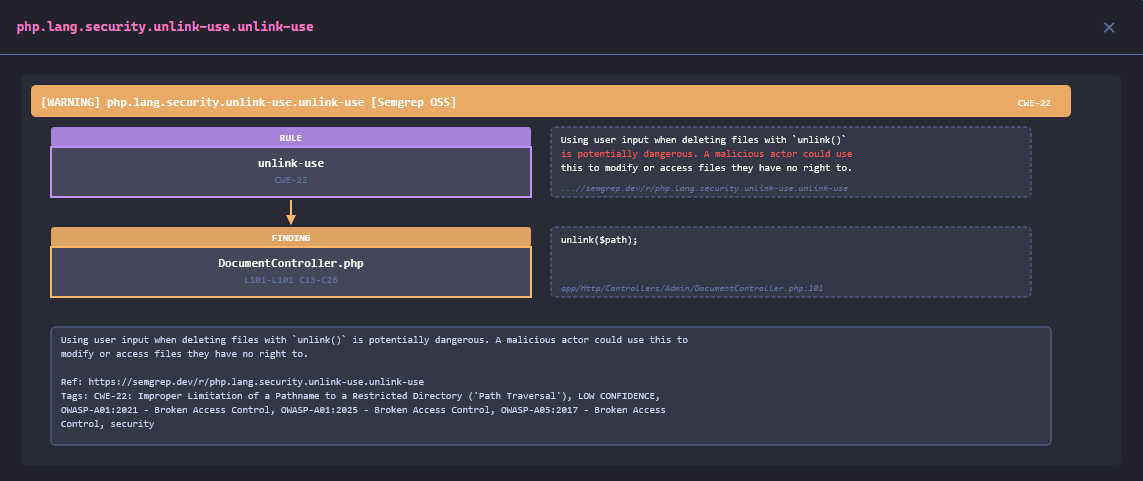
Clicking “Graph” on a finding opens a detailed view showing the rule-to-finding flow, the associated CWE, the code snippet, and a full description with references and OWASP tags:
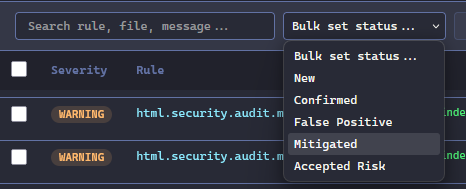
Bulk operations let you update the status of multiple findings at once, with lifecycle states like New, Confirmed, False Positive, Mitigated, and Accepted Risk:
Compatible tools
The tool has been tested with several popular static analysis and secret detection tools:
- Semgrep / Opengrep — static analysis
- CodeQL — GitHub’s code scanning engine
- Snyk — vulnerability scanner
- Gitleaks — secret detection in git repos
- Trufflehog — secret detection across multiple sources
Any tool that outputs valid SARIF should work out of the box.
Features
- SARIF file upload — drag-and-drop support with automatic parsing
- Multi-file projects — upload multiple SARIF files into the same project; findings are merged with automatic deduplication
- Finding management — browse, filter, and search findings by severity, status, rule ID, file path, message, or code snippet
- Status tracking — track findings through their lifecycle: New, Confirmed, False Positive, Mitigated, Accepted Risk
- Annotations — add notes to individual findings for documentation and collaboration
- SVG visualizations — generated graphs showing rule information, code flows (source to sink), and locations
- Bulk operations — update the status of multiple findings at once
- SARIF export — export findings back to SARIF format with embedded review status and notes
- Multi-project support — manage multiple SARIF uploads as separate projects
- REST API — all features are accessible via a REST API, making it easy to integrate sarif2web into your CI/CD pipeline or automation scripts
Result
At the time of writing this article, sarif2web is available on my GitHub: sarif2web
You can deploy it via Docker and import sarif files. Each time you edit the status of a finding, it is stored in a MongoDB database so that you can return to it later without having to re-sort.
What’s next?
This is just the beginning. Here are some ideas I’m exploring:
- Support for additional static analysis formats beyond SARIF
- Link to the code base that triggered the alert
- Markdown/PDF export
The tool is open source and built to evolve. If you have ideas, feedback, or want to contribute, feel free to reach out on Discord (hadzah) or open a pull request on the repo.